Back
BackChapter 4: Internal Control and Cash – Financial Accounting Study Notes
Study Guide - Smart Notes

Internal Control and Cash
Fraud and Its Impact
Fraud is a deliberate misrepresentation of facts intended to persuade another party to act in a way that causes injury or damage. It is a growing concern globally, especially with the rise of e-commerce. Fraud can take many forms, including insurance fraud, check forgery, Medicare fraud, credit card fraud, and identity theft.
Misappropriation of assets: Typically committed by employees, involving theft of money or inventory, bribery, kickbacks, or overstated expense reimbursements.
Fraudulent financial reporting: Usually committed by managers, involving false or misleading journal entries to deceive investors and creditors.
Ethical and legal implications: Fraud is illegal and unethical, resulting in penalties such as imprisonment, fines, and damages. It violates the rights of many for the temporary gain of a few.
Example: An employee overstates their expense reimbursement, causing financial loss to the company.
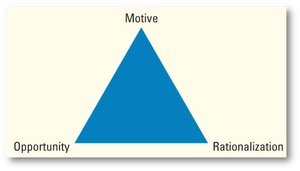
Additional info: The Fraud Triangle illustrates the three elements necessary for fraud: motive, opportunity, and rationalization.
Objectives and Components of Internal Control
Internal control is the primary method for preventing, detecting, and correcting fraud. It consists of a plan of organization and procedures designed to achieve five objectives:
Safeguard assets
Encourage employees to follow company policy
Promote operational efficiency
Ensure accurate, reliable accounting records
Comply with legal requirements
Additional info: Management is responsible for establishing and maintaining adequate internal controls over financial reporting, as required by law and accounting standards.
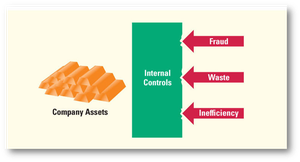
Additional info: Internal controls act as a barrier to protect company assets from fraud, waste, and inefficiency.
Components of Internal Control
The internal control system is composed of several key components:
Control Environment: The tone at the top, including the code of ethics.
Risk Assessment: Identifying business risks and establishing procedures to address them.
Information System: The means by which accounting information enters and exits the system, tracking assets, profits, and losses.
Control Procedures: Methods to achieve the objectives of internal control.
Monitoring of Controls: Ongoing review, often through technology and audits.
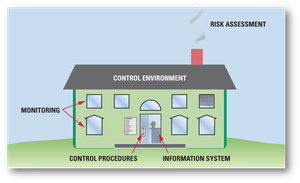
Additional info: The diagram visually represents the components of internal control as parts of a house, emphasizing their interconnectedness.
Internal Control Procedures
Effective internal control procedures include:
Smart Hiring Practices: Background checks, training, supervision, competitive salaries, and clear responsibilities.
Separation of Duties: Dividing asset handling, record keeping, and transaction approval among different employees.
Comparison and Compliance Monitoring: Use of budgets, exception reporting, and audits.
Adequate Records: Maintaining detailed, prenumbered documents, either hard copy or electronic.
Limited Access: Restricting access to assets based on job responsibilities, using physical and digital controls.
Proper Approvals: Requiring management approval for transactions, often delegated to specific departments.
Example: Only the purchasing department can buy from approved vendors, based on competitive bids.
Information Technology and Safeguard Controls
Modern accounting systems increasingly rely on information technology, improving accuracy and speed. Safeguard controls include fireproof vaults, security cameras, loss prevention specialists, fidelity bonds, mandatory vacations, and job rotation.
Internal Controls for E-Commerce
E-commerce introduces risks such as stolen credit card numbers, malware, and phishing. Security measures include encryption and firewalls.
Encryption: Rearranges messages mathematically so only authorized parties can read them.
Firewalls: Limit unauthorized access to computer networks, requiring passwords and PINs.
Example: Customer account numbers use check-sum digits to detect errors.
Internal Controls Over Cash Receipts and Payments
Cash is highly susceptible to theft, requiring specific internal controls.
Cash Receipts Over the Counter: Point-of-sale terminals record sales, inventory reduction, and issue receipts. Cash drawers are reconciled and deposited.
Cash Receipts by Mail: Mailroom staff process checks and remittance advice, which are then handled by the treasurer, accounting department, and controller.
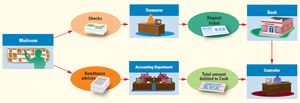
Additional info: The diagram shows the flow of checks and remittance advice from mailroom to bank and accounting department.
Controls Over Payment by Check: Most payments are made by check or EFT, providing a record, requiring authorized signatures, and supporting evidence.
Controls Over Purchase and Payment: Duties are split among purchasing, receiving, preparing payment, and approving payment.
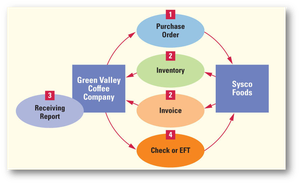
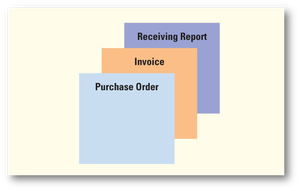
Additional info: The payment packet includes purchase order, invoice, and receiving report, supporting the payment process.
Limitations of Internal Control
Internal controls can be circumvented by collusion, management override, or human limitations such as fatigue and negligence. The benefits of internal controls should always outweigh their costs.
Bank Reconciliation
Bank reconciliation explains differences between the company’s cash records and the bank balance, often due to timing differences.
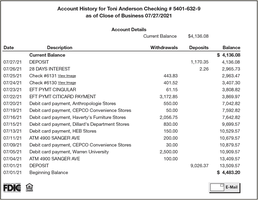
Documents used: Signature card, deposit ticket, check, bank statement, bank reconciliation.
Check: Involves three parties: maker, payee, and bank.
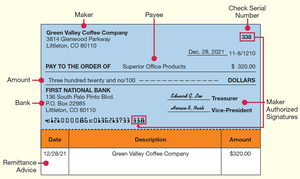
Additional info: The check diagram shows the maker, payee, bank, amount, and remittance advice.
Bank Statement: Sent monthly, showing beginning and ending balances, receipts, and payments.
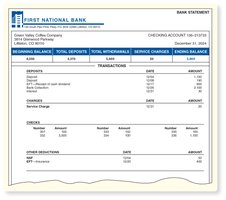
Bank Reconciliation: Adjusts for deposits in transit, outstanding checks, bank errors, bank collections, EFTs, service charges, interest, NSF checks, and book errors.
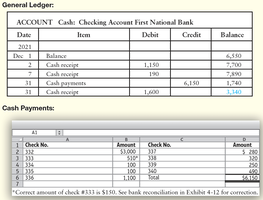
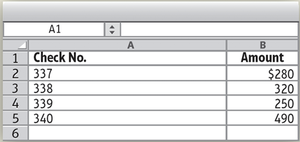
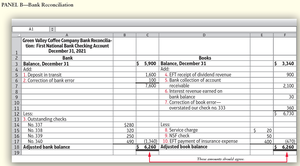
Additional info: The reconciliation table shows adjustments to both bank and book balances, ensuring they match after corrections.
Reporting Cash on the Balance Sheet
Cash and cash equivalents are reported on the balance sheet. Cash equivalents include time deposits, certificates of deposit, and high-grade government securities close to maturity.
Footnote disclosure: Highly liquid investments with maturities of three months or less are classified as cash equivalents.
Summary Table: Bank Reconciliation Items
Bank Balance | Book Balance |
|---|---|
Add deposits in transit | Add bank collections, interest, EFT receipts |
Subtract outstanding checks | Subtract service charges, NSF checks, EFT payments |
Add/Subtract bank errors | Add/Subtract book errors |
Online Banking
Online banking provides real-time access to account history, facilitating reconciliation and monitoring of cash transactions.